In the article What Is Cloud Phone, a cloud phone is defined as a real Android device running on the cloud. But where does "real" begin? The answer lies in ISA — Instruction Set Architecture. Every processor executes a fixed instruction set, and when you run an Android app on an x86 emulator, that app must pass through a binary translator to convert instructions. Anti-cheat systems inspect which instruction set the chip executes to distinguish real devices from emulators.
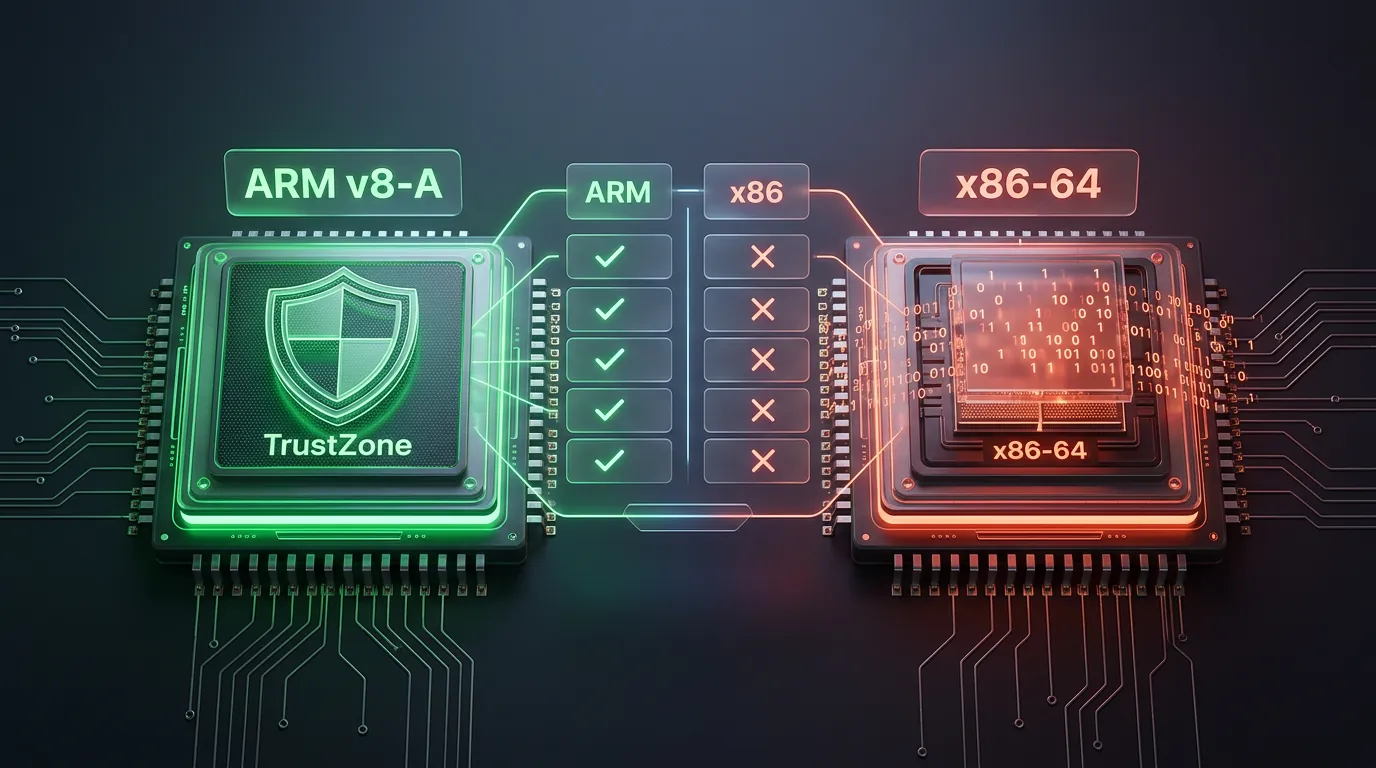
ARM v8-A ISA includes 4 instruction-level security features — TrustZone, MTE, PAC, and fixed-width instructions — that x86 binary translation cannot replicate. This article analyzes what ISA is, 4 ARM features that create a genuine hardware fingerprint, 3 risk layers of binary translation, 5 anti-cheat methods that exploit ISA differences, and why ARM cloud phones eliminate all detection signals.
What Is ISA — The Hardware Instruction Set That Defines a Processor
ISA (Instruction Set Architecture) is the hardware instruction set that defines how a processor communicates with software. Each ISA specifies how the CPU reads, decodes, and executes instructions — the instruction set a chip uses from the moment it is manufactured.
The two most prevalent ISAs today are ARM v8-A (AArch64) and x86-64. ARM v8-A powers over 99% of mobile chips, from Qualcomm Snapdragon, Samsung Exynos, to MediaTek Dimensity. x86-64 dominates the desktop and server landscape, powering Intel Core and AMD Ryzen processors.
When Android apps are compiled, the compiler generates machine code targeting a specific ISA. Apps compiled for ARM v8-A contain AArch64 instructions. Running an ARM app on an x86 chip requires binary translation — a software layer that converts each ARM instruction into an equivalent x86 instruction.
An important distinction: chip architecture (RISC vs CISC) ≠ ISA instruction set (this article) ≠ code translation mechanism (JIT/AOT). ISA is the intermediate layer — sitting between the physical architecture and the translation software.
3 notable ISAs in the mobile ecosystem: ARM v8-A (Android standard), x86-64 (desktop emulators), and RISC-V (emerging for IoT). In the cloud phone context, ISA determines whether a device runs Android's native instruction set or requires binary translation — the core factor that anti-cheat systems inspect.
ARM v8-A (AArch64) — 4 ISA Features That Create a Genuine Fingerprint
ARM v8-A ISA includes 4 instruction-level security features that x86 binary translation cannot replicate. Each feature operates at the hardware level, producing a fingerprint that emulation software cannot perfectly reproduce.
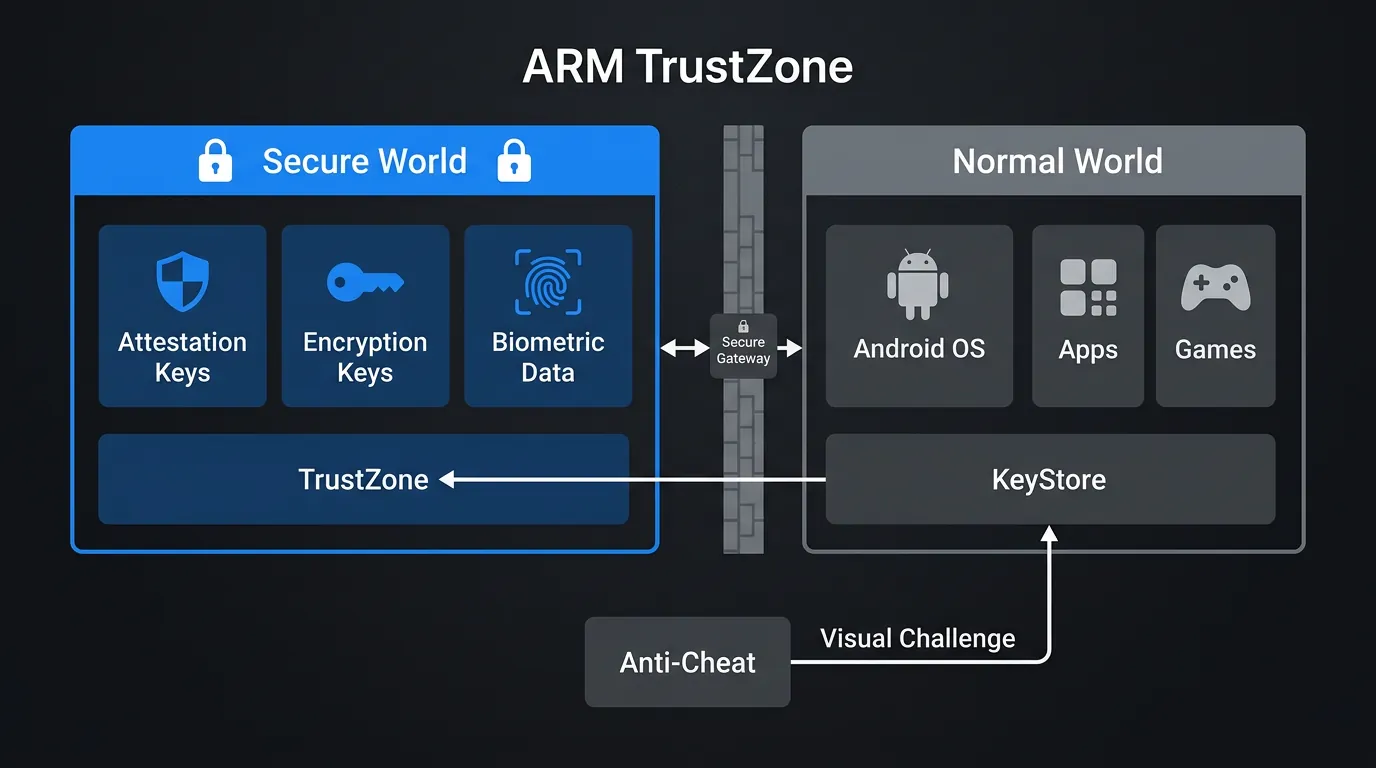
TrustZone — A Parallel Security World
TrustZone creates a hardware-isolated secure execution environment (Secure World) that runs in parallel with the main operating system (Normal World). Inside the Secure World, TrustZone stores attestation keys, encryption keys, and biometric data — all protected by silicon, not software.
Anti-cheat and authentication platforms use Android KeyStore Hardware Attestation to verify devices. The process works as follows: the app sends a challenge → KeyStore forwards it to TrustZone → TrustZone signs the response with a hardware-bound key → the app verifies the signature.
x86 emulators lack TrustZone hardware. When receiving a challenge from KeyStore Hardware Attestation, emulators return a software-backed key instead of a hardware-backed key — a difference detection systems identify immediately.
Software can emulate the TrustZone API interface, but cannot produce a hardware-bound key embedded in silicon — a difference the attestation protocol catches at the verify step.
Memory Tagging Extension (MTE) and Pointer Authentication Code (PAC)
MTE (introduced in Armv9) protects memory with a 4-bit tag system assigned to every 16 bytes of memory. When the CPU accesses a memory cell, MTE compares the pointer tag against the memory tag — a mismatch triggers an immediate fault. This mechanism detects buffer overflows, use-after-free vulnerabilities, and memory errors with less than 3% performance overhead.
PAC (Pointer Authentication Code, from Armv8.3) authenticates return addresses using hardware keys. Each time a function is called, PAC appends a signature to the pointer. When the function returns, the CPU verifies the signature — if tampered with, the CPU refuses execution. PAC defeats ROP (Return-Oriented Programming) and JOP (Jump-Oriented Programming) — the 2 most common attack techniques.
Binary translation cannot replicate MTE and PAC at the hardware level. x86 has DEP (Data Execution Prevention) and ASLR (Address Space Layout Randomization), but these are software-based measures — operating at a different layer and producing different response patterns when anti-cheat inspects. Missing MTE/PAC responses = a clear detection signal.
MTE operates at the silicon level with less than 3% performance cost — emulation software cannot replicate tag comparison at hardware cycle speeds.
Fixed-Width Instructions and Predictable Timing
ARM v8-A uses fixed 32-bit instructions — every instruction has the same size. The CPU decodes instructions through a uniform pipeline, producing stable and predictable timing patterns.
x86-64 uses variable-length instructions ranging from 1 to 15 bytes. The CPU must determine each instruction's size before decoding, creating more complex timing patterns. When binary translation converts 32-bit ARM instructions into variable-length x86 instruction sequences, micro-delays appear — each instruction adds 2–5 nanoseconds of overhead.
Anti-cheat systems measure instruction timing using high-resolution timers (rdtsc on x86, cntvct_el0 on ARM). On real ARM devices, timing patterns hold steady with variance below 5 nanoseconds. Under binary translation, timing fluctuates 15–30 nanoseconds per instruction — accumulated micro-delays produce a distinctive timing map that ML models detect.
3 Risk Layers of x86 Binary Translation — From an ISA Perspective
x86 binary translation produces 3 layers of artifacts at the ISA level, each serving as a detection signal for anti-cheat. These artifacts exist at multiple levels, ranging from easy to spoof to completely impossible.
ELF Header — The Immutable Architecture Record
Every Android executable (executable, shared library) contains an ELF header specifying the target architecture. The e_machine field identifies the ISA: EM_AARCH64 (0xB7) for ARM 64-bit, EM_386 (0x03) for x86 32-bit, EM_X86_64 (0x3E) for x86 64-bit. This field is set at compile time and embedded in the binary — it is not a runtime configuration value.
Anti-cheat can read the ELF header of libc.so, libandroid_runtime.so, or any system library. On x86 emulators, native libraries contain x86 ELF headers — regardless of whether the emulator has spoofed cpuinfo to report "arm64-v8a." A single check of one system library reveals the true ISA underneath the spoofed surface layer.
cpuinfo and Build.HARDWARE CAN be spoofed via software. System library ELF headers CANNOT be modified without breaking the entire operating system — because the OS must execute the correct architecture to function. Changing ELF headers would require recompiling every system binary for a different architecture, which fundamentally breaks the execution environment.
Instruction Timing and System Call Patterns
Houdini (Intel) and libhoudini (Google) are the 2 most common binary translators, converting ARM instructions to x86 in real time. Each translated ARM instruction adds 2–5 nanoseconds of micro-latency. At an average of 1 billion instructions per second, accumulated micro-latency produces a measurably different timing profile.
System call sequences on native ARM and translated ARM-on-x86 also differ. When calling mmap(), ioctl(), or openat(), the order and timing between syscalls on native ARM follow a fixed pattern. Binary translation adds more overhead to some syscalls than others — creating a distinctive syscall timing fingerprint.
GPU instruction sets also serve as signals: ARM SoCs use Mali (ARM) or Adreno (Qualcomm) GPUs, while x86 emulators use Intel HD/UHD or virtualized GPUs. Shader compilation, texture sampling, and render pipeline behavior produce an entirely different GPU fingerprint.
Why Spoofing ISA Information Is Ineffective
Spoofing ISA information operates at 3 layers, each harder than the last:
- cpuinfo layer (easy to fake): Modify
/proc/cpuinfo,Build.CPU_ABI,Build.HARDWARE→ basic anti-cheat is fooled, but advanced anti-cheat ignores cpuinfo - ELF header layer (extremely difficult): Requires modifying the header of every shared library → breaks dynamic linking, OS crashes
- TrustZone attestation layer (impossible): Hardware-bound keys cannot be cloned via software → unforgeable
Conclusion: binary translation produces artifacts at every inspection layer. An emulator can conceal one layer, but defeating all 3 simultaneously is impossible.
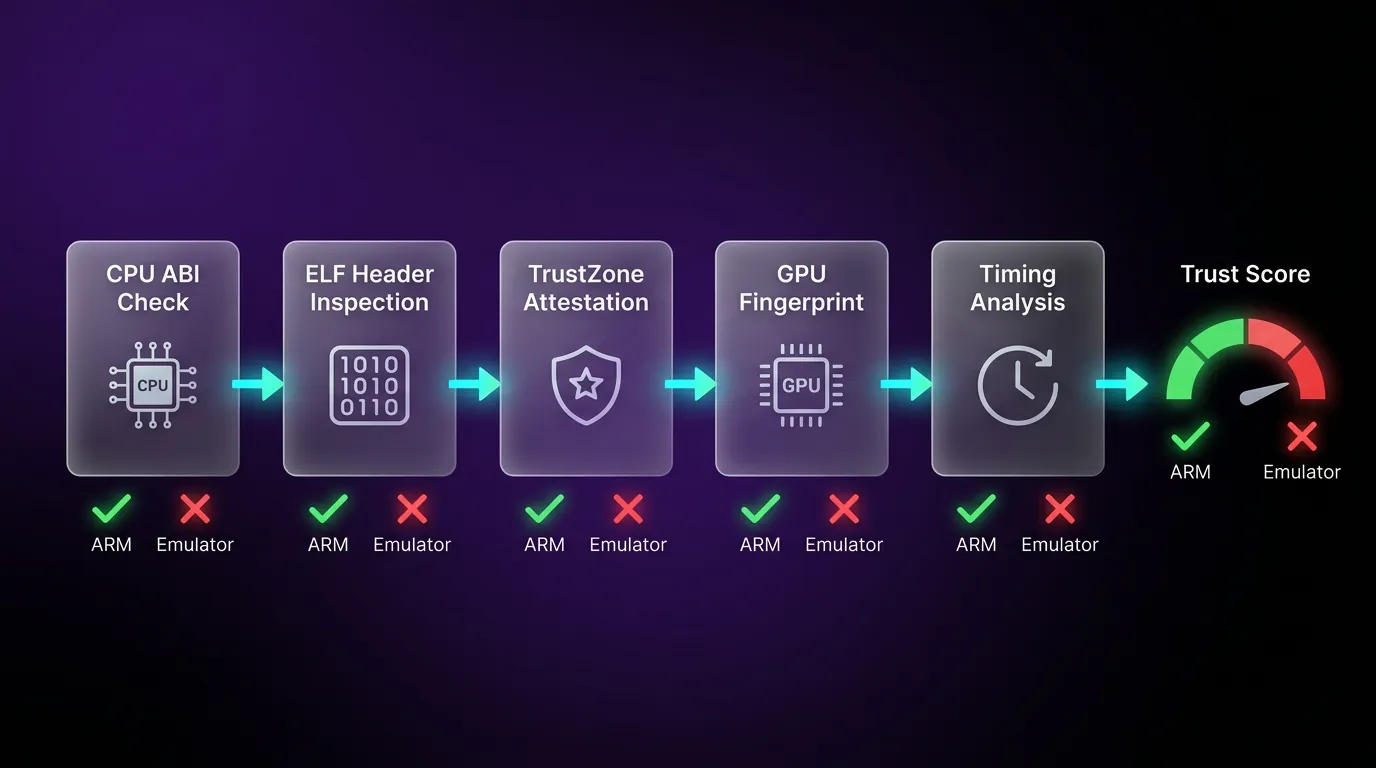
Anti-Cheat ISA Exploitation — 5 Detection Methods
Anti-cheat exploits ISA differences through 5 detection methods that binary translation cannot fully conceal. Methods are ordered from simplest to most complex:
- Check CPU ABI string — read
Build.SUPPORTED_ABISto confirmarm64-v8a. Emulators typically returnx86_64or a spoofed value inconsistent with other signals - Inspect ELF binary headers — read the
e_machinefield of/system/lib64/libc.so. Value 0xB7 (AARCH64) on real ARM, 0x3E (X86_64) on emulators — cannot be modified without breaking the system - Validate TrustZone-backed KeyStore attestation — send a challenge to Android KeyStore, requesting a hardware-backed certificate chain. Emulators return software attestation instead of hardware attestation
- Analyze GPU instruction set — check GPU drivers (Mali, Adreno vs Intel HD). Shader compilation behavior and supported extensions differ between mobile and desktop GPUs
- Measure instruction execution timing — use high-resolution timers to measure latency of specific instruction sequences. Binary translation adds micro-delays measurable through statistical analysis
Combining all 5 methods, detection systems identify binary translation with over 95% accuracy, according to Build38's emulator detection research. Modern anti-cheat systems including GameGuard, EasyAntiCheat, and BattlEye use at least 3 of these 5 methods.
From ISA technicalities to real-world impact: what benefits does native ISA deliver when running a cloud phone?
Real ARM Cloud Phone — Zero Translation, Zero Detection Signal
An ARM cloud phone runs the native ISA, eliminating all 3 artifact layers that binary translation creates. When apps execute on a real ARM chip, every instruction runs directly — no translation layer, no micro-delay, no mismatched ELF headers. The device presents itself to every inspection method exactly as a standard handheld Android phone would.
3 real-world scenarios demonstrate native ISA advantages:
Gaming (Anti-cheat pass): Games like Genshin Impact, PUBG Mobile, and Free Fire use anti-cheat that inspects ISA. An ARM cloud phone passes all 5 detection methods described above — because the real chip returns correct ISA values, genuine TrustZone responses, and native timing patterns. Players experience zero interruptions from anti-cheat false positives that plague emulator users.
Social Media (High Trust Score): Platforms like Facebook, TikTok, and Instagram collect device attestation data including ISA verification. ARM devices pass hardware attestation → positive Trust Score signal → fewer checkpoints and verifications. Accounts running on real ARM hardware build trust faster and maintain higher standing over time.
Banking/Finance (Hardware attestation): Banking apps require hardware-backed KeyStore. An ARM cloud phone with TrustZone returns a valid certificate chain — x86 emulators cannot do this. Financial apps that refuse to run on emulators function normally on ARM cloud phones.
Emulators like BlueStacks, LDPlayer, and NoxPlayer run on x86 ISA → fail at least 3 of 5 checks. VMI (Virtual Mobile Infrastructure) cloud phones from some competitors run on x86 servers → also fail TrustZone and ELF checks. XCloudPhone uses the Exynos 8895 — a real ARM chip with native v8-A ISA, genuine TrustZone, and authentic timing patterns.
XCloudPhone costs ~$10/device on a pay-as-you-go model, significantly reducing the risk of detection and account restrictions compared to traditional emulators. For phone farm operations running dozens of accounts, a real cloud phone with native ISA delivers undetectable device profiles at scale.
👉 Experience a real cloud phone at app.xcloudphone.com
ISA and Trust Score — How Instruction Sets Determine Device Trust
ISA-level features contribute directly to Trust Score by producing genuine hardware signals that platforms collect to evaluate devices.
Trust Score aggregates multiple signal sources, with ISA influencing 3 primary components:
- Hardware Attestation: TrustZone-backed KeyStore certificate → the strongest signal. Hardware attestation carries high weight in Trust Score because it is unforgeable
- Instruction Timing: Fixed-width ARM timing patterns match the baseline of real devices → positive signal. Emulators produce timing anomalies → negative signal
- GPU Fingerprint: Mali/Adreno GPU instructions → match the mobile device database. Intel HD/AMD GPU → match the desktop database → anomalous signal
The complete trust chain: native ISA (this article) → sensor data consistency (sensor data verification) → network fingerprint (network identity) → overall Trust Score. Each layer adds trust points — an ARM cloud phone with native ISA gains an advantage from the very first layer.
FAQ — ISA and Cloud Phone Safety
"Is ARM or x86 ISA better suited for Android?"
ARM ISA is better suited because Android is designed to run natively on ARM. The NDK, framework, and most apps compile for ARM v8-A. Running Android on x86 requires binary translation, adding 15–30% performance overhead and detection signals.
"Can emulators fake ISA information?"
Emulators can fake the cpuinfo layer, but cannot fake ELF headers or TrustZone. The cpuinfo layer (Build.CPU_ABI) is easy to spoof. System library ELF headers are extremely difficult to modify. TrustZone hardware attestation is impossible to forge because the key is permanently embedded in silicon.
"Does an ARM cloud phone pass Play Integrity?"
ARM cloud phones pass Play Integrity at the MEETS_DEVICE_INTEGRITY level — the highest level for certified devices. A real ARM chip with TrustZone, a valid bootloader, and full CTS (Compatibility Test Suite) compliance produces a response identical to a handheld phone.
"Does every ARM chip include TrustZone?"
Not every ARM chip includes TrustZone — TrustZone is an optional feature in the ARM specification. However, most mobile SoCs from 2014 onward (Cortex-A53 and newer) integrate TrustZone. ARM IoT chips and microcontrollers often lack this feature.
From ISA to Choosing a Cloud Phone — The Complete Picture
ISA determines which instruction set a chip executes — and anti-cheat, social platforms, and banking apps all inspect that instruction set. ARM v8-A ISA includes TrustZone, MTE, PAC, and fixed-width instructions that produce a hardware fingerprint binary translation cannot replicate.
An ARM cloud phone executes Android's native ISA — zero translation, zero artifacts, zero detection signals. This is the first layer in the Trust Score chain, followed by sensor data consistency (how sensor data confirms a real device) and network fingerprint (how network identity completes the trust picture).
Every trust chain starts at ISA — the physical foundation of trust. Learn more about what a cloud phone is in the overview article What Is Cloud Phone, or explore how ARM differs from x86 at the architecture level in ARM vs x86.
👉 Start your real ARM cloud phone experience: app.xcloudphone.com